Table IV from Automated security configuration checklist for a cisco IPsec VPN router using SCAP 1.2 | Semantic Scholar

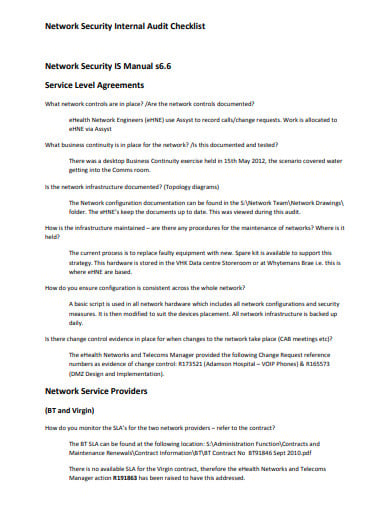
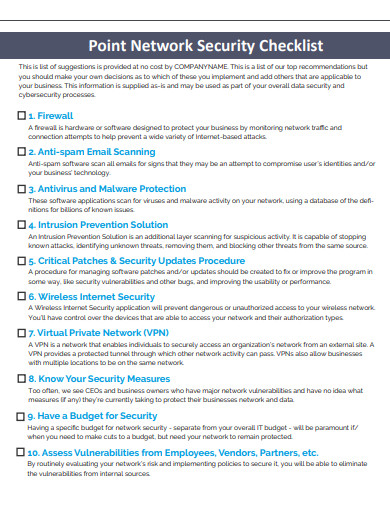
Information Security Audit Checklist Template for Businesses (13 Samples) - Template Sumo | Security audit, Audit, Checklist template
![A Web Application Security Checklist - Hacking Exposed Web Applications, Third Edition, 3rd Edition [Book] A Web Application Security Checklist - Hacking Exposed Web Applications, Third Edition, 3rd Edition [Book]](https://www.oreilly.com/api/v2/epubs/9780071740647/files/t0414-02.jpg)


![The Sensible Small Business IT Security Checklist 2019 [Infographic] | iFeeltech The Sensible Small Business IT Security Checklist 2019 [Infographic] | iFeeltech](https://ifeeltech.com/wp-content/uploads/2017/12/THE-SENSIBLE-SMALL-BUSINESS-IT-CHECKLIST.png)



![AAA SECURITY CHECKLIST ACCESS [11] | Download Table AAA SECURITY CHECKLIST ACCESS [11] | Download Table](https://www.researchgate.net/publication/267961211/figure/tbl2/AS:668861271666699@1536480362651/AAA-SECURITY-CHECKLIST-ACCESS-11.png)